A community-led forensic investigation links the attacks to a reported breach of 21 million records from PrestaShop’s own Addons Marketplace.
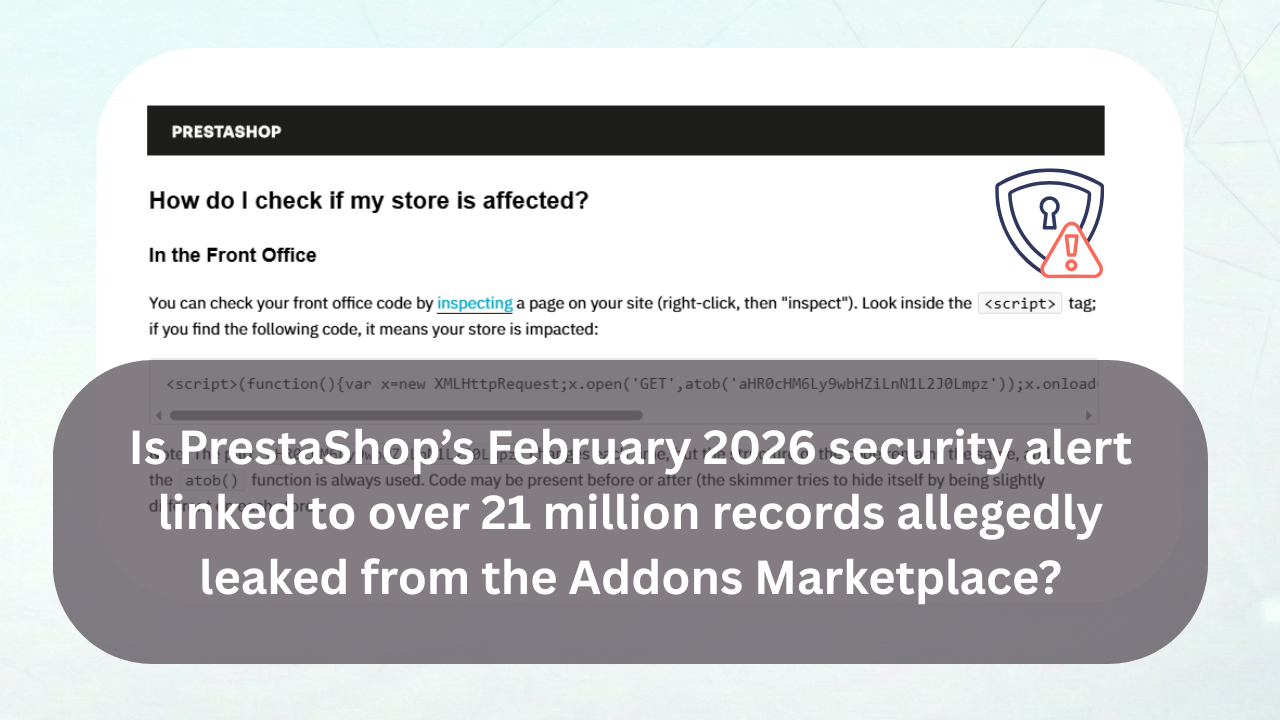
PrestaShop has not confirmed or denied the connection, only issued a security alert on February 12, 2026, notifying merchants that a digital skimmer is actively replacing payment buttons on checkout pages with fraudulent duplicates.
When customers click the fake buttons, they are redirected to a fake payment form that captures their card data.
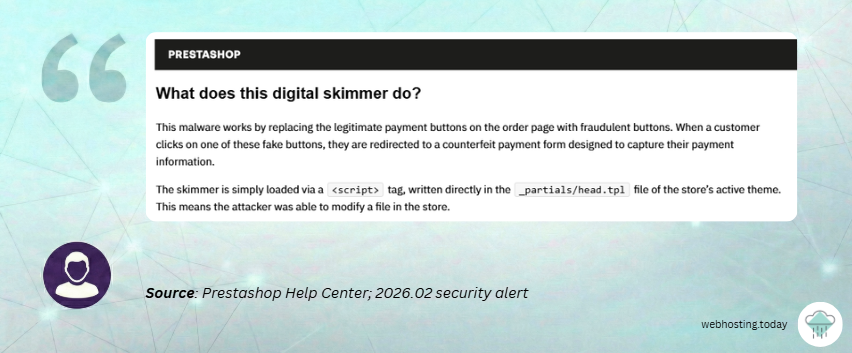
The initial alert was brief. It told merchants to check a specific template file, look for suspicious modules, change their passwords, and consult GDPR obligations.
What the community found out about the attacks
The PrestaShop alert contains no root cause analysis, it does not explain how attackers gained write access to store files.
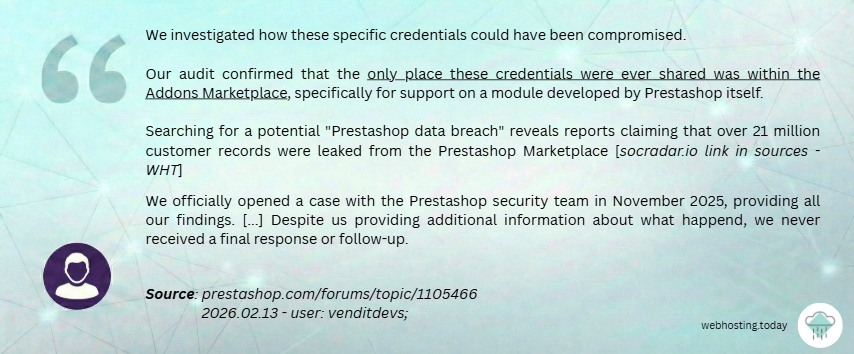
The community reaction was immediate – on the PrestaShop forum, developer “venditdevs” published a forensic breakdown of an affected store he maintains.
According to him, credentials used to attack the store could be compromised only through PrestaShop’s own Addons Marketplace.
This conclusion of “venditdevs” and other users might have strong foundations, as it’s consistent with how the Marketplace support process works.
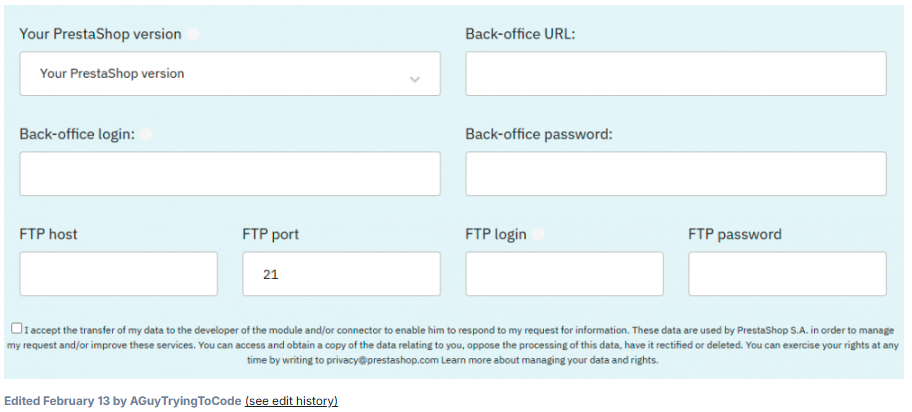
When a merchant opens a support ticket for a module, PrestaShop’s ticketing system requests:
- back-office URL,
- back-office login and password,
- FTP host, port, login, and password,
- PrestaShop version.
A screenshot of this form was shared in the forum thread by another user, “AGuyTryingToCode” who raised the obvious question: what happens to these credentials after the support ticket is closed, who has access to them and how are they stored?
According to “venditdevs”, his search for potential “PrestaShop data breach” led him to a few reports (e.g. on breach monitoring service SOCradar.io from August 2025) that are claiming that “over 21 million customer records were leaked from the PrestaShop Marketplace”:
Venditdevs also claims that he reported these findings to PrestaShop’s security team in November 2025. According to him the team said they were investigating, no follow-up was provided, and now, three months later, other stores started getting hit.
What can be done by hosting providers
PrestaShop powers more than 300,000 online stores, a significant share of which run on shared hosting infrastructure.
If the Addons Marketplace is confirmed as the source of stolen credentials, this is not a software vulnerability that can be patched, but a supply-chain breach. In such a scenario the compromised data didn’t come from a bug in PrestaShop’s code, but from credentials merchants submitted through the platform’s own support system.
For hosting providers, there is a narrow window of opportunity here. The malware signatures from PrestaShop’s alert, rogue modules and injected scripts, are detectable at the infrastructure level through standard scanning tools. Providers who act now can identify and warn affected merchants ahead of PrestaShop’s own communication, which forum users described as “useless without root cause” and “a joke.”
The broader question is one of trust. If a platform vendor’s marketplace becomes the attack vector, the traditional assumption that keeping software updated equals staying secure no longer holds. Hosting providers may need to factor supply-chain risk into how they support and advise merchants running platforms with centralized add-on ecosystems.
If the Addons Marketplace will be confirmed as the source of stolen credentials of over 21 million customers of PrestaShop powered stores, this will not be a software vulnerability that can be patched, but a serious supply-chain breach.
For hosting providers, the implications are operational, as the malware signatures mentioned in the PrestaShop’s alert are scannable at the infrastructure level (“mloader,” “simplefilemanager,” and the atob() script pattern in .tpl files).
Perhaps it’s worth checking if more customers can be identified and warned ahead of PrestaShop’s own communication, which forum users described as “useless without root cause” and “a joke“.
As of this writing, PrestaShop has not publicly addressed the alleged Marketplace data leak, nor explained how attackers obtained valid store credentials. Until that happens, the root cause remains an open question and so does the exposure for every merchant and hosting provider in the ecosystem.
Sources:
1. PrestaShop Help Center: “Security Alert – Recommended Check of Your Stores” (February 2026).
2. PrestaShop Forums: “Recent PrestaShop securtity alert” – post of user: venditdevs; (February 13, 2026).
3. SOCRadar: PrestaShop data breach report from August 2025.
Damian Andruszkiewicz
Author of this post.