CVE-2026-41940 is moving fast enough that a new article every few hours would do more to clutter your inbox than to inform you. We are keeping this page updated instead. The most recent updates appear at the top. For the full background, see our original April 29 coverage and our May 3 follow-up on the 64-day zero-day window. cPanel has not responded to webhosting.today’s questions about the disclosure timeline.
Latest Updates
May 4, 2026 — Update 8
TechCrunch reports the Shadowserver count of likely compromised IPs has fallen further, to approximately 2,000 as of May 4, down from 3,540 on May 3 and 44,000 on April 30. The decline tracks with the patch cycle completing across major providers. TechCrunch also cites WebPros, cPanel’s parent company, putting the total number of domains running on cPanel and WHM infrastructure at 60 million, providing an official vendor figure alongside watchTowr’s earlier estimate of approximately 70 million. Finally, TechCrunch notes that Google indexed dozens of compromised sites displaying attacker ransom messages, making the scale of Sorry Ransomware deployment visible in public search results.
May 4, 2026 – Update 7
Help Net Security reports two updated figures as of May 4. First, the Censys count of hosts with open directories exposing .sorry file extensions has risen to 8,859 total hosts, with 7,135 of those confirmed as running cPanel or WHM. Second, Shadowserver data shows the number of compromised IPs actively scanning, running exploits, or brute-forcing fell from 44,000 on April 30 to 3,540 by May 3, consistent with the patch cycle completing across major providers. The decline reflects remediation progress, not the end of active campaigns.
Help Net Security also notes a tactic observed in ransomware deployments not previously reported: attackers were wiping server backups before or during encryption to prevent recovery without paying the ransom. Operators who relied on local backups stored on the same compromised server should assume those backups are gone.
May 4, 2026 – Update 6
Ctrl-Alt-Intel has published the full technical report on the Southeast Asia campaign, and it contains considerably more detail than the initial summary from The Hacker News. The threat actor targeted specific named entities: Philippine Coast Guard, Philippine Air Force 15th Strike Wing, Philippine Government Arsenal (Department of National Defense), Lao Ministry of National Defence, and Lao Ministry of Natural Resources and Environment, alongside a set of MSPs and hosting providers in the Philippines, Laos, Canada, South Africa, and the United States.
The more significant finding is what the exposed C2 server revealed beyond the cPanel campaign. The same actor had already conducted a separate operation in March 2026, weeks before CVE-2026-41940 was publicly known, exfiltrating 110 files (~4.37GB) from the China Railway Society Electrification Committee, a body operating under the China Railway Society which explicitly commits to CCP leadership. The stolen files span 2020 to 2024 and include conference materials, engineering documents on traction power and high-speed rail systems, and two payment workbooks containing names, PRC national ID numbers, bank account numbers, and phone numbers.
The actor also deployed a custom SQLi exploit chain against an Indonesian defence-sector training portal, bypassing its CAPTCHA by reading the expected value from the server-issued session cookie, then escalating a SQL injection to RCE via PostgreSQL’s COPY ... TO PROGRAM capability.
For persistence, the actor used a masqueraded systemd service named systemd-update.service, with the Ligolo reverse tunnel payload hidden at /usr/local/bin/.netmon/systemd-helper. C2 ran over delicate-dew.serveftp[.]com:4455. Ctrl-Alt-Intel notes Vietnamese comments throughout the actor’s Python tooling but explicitly does not attribute the campaign to any specific country, noting the comments could be a deliberate false flag.
The picture this paints: CVE-2026-41940 was one opportunistic addition to the toolkit of a threat actor that had already been conducting regional collection operations for months. The cPanel vulnerability lowered the cost of initial access; the broader operation predates it.
May 4, 2026 – Update 5
Forensic analysis published by I Am Tzar of confirmed CVE-2026-41940 compromises documents four persistence mechanisms deployed by attackers after gaining WHM access. First, attacker-controlled ed25519 public keys appended to /root/.ssh/authorized_keys for password-less backdoor access surviving password resets. Second, a 964 KB ELF binary dropped at /usr/bin/.system_cache with the SUID bit set, hidden from standard ls listings by a leading dot, enabling instant root escalation from any user account. Third, daily callback scripts written to /etc/cron.daily/cpanel_sync that fetch updated payloads from command-and-control servers. Fourth, malicious droppers appended to /root/.bashrc, re-executing on every interactive administrator login.
The practical implication is the same point NocInit made earlier: a server compromised at WHM level cannot be assumed clean after manual cleanup. These persistence mechanisms are specifically designed to survive patching, password rotation, and partial remediation. Migration to a clean installation from pre-breach backups remains the only reliable remediation for confirmed compromises.
May 4, 2026 – Update 4
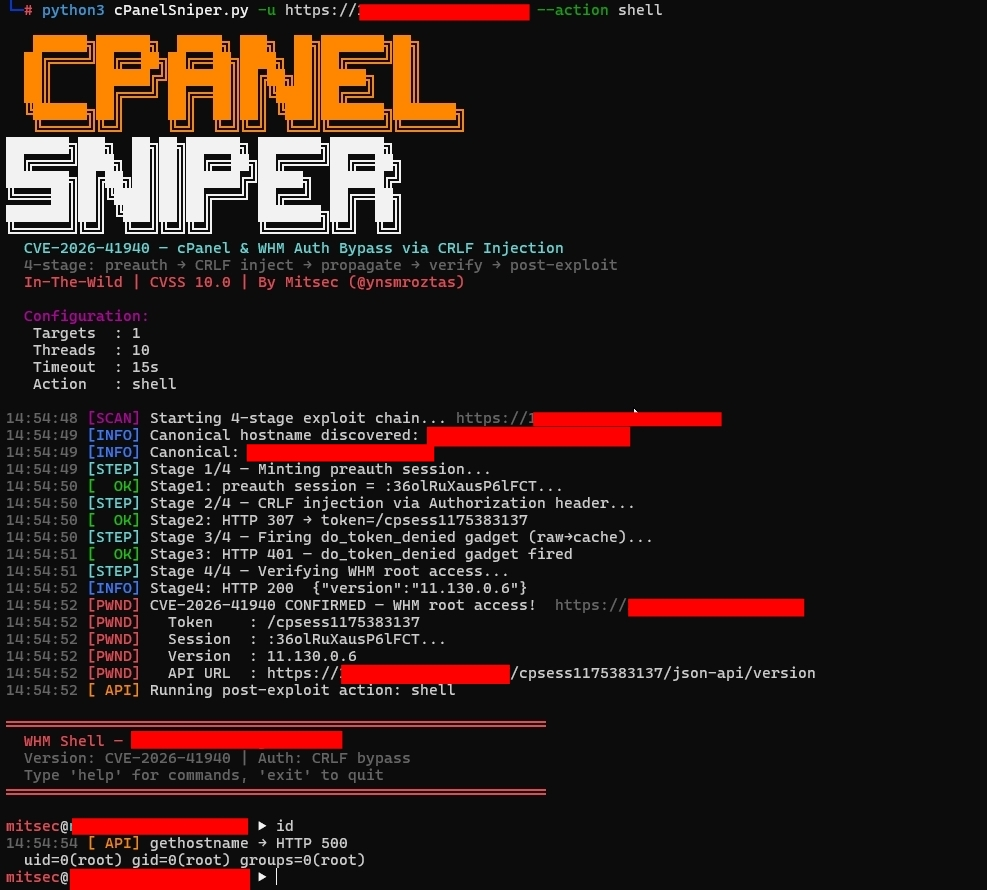
A public exploitation framework for CVE-2026-41940 named cPanelSniper has been published on GitHub by researcher ynsmroztas. The tool is a pure Python implementation requiring no external dependencies and implements the full four-stage exploit chain: canonical hostname discovery, pre-authenticated session creation, CRLF payload injection, and session verification. Post-exploitation capabilities include an interactive WHM shell, bulk account listing, remote command execution, password modification, and creation of backdoor administrator accounts. The tool supports threaded bulk scanning across multiple targets. Its availability on a public repository means exploitation of any remaining unpatched cPanel instance now requires minimal technical skill. If you have not yet patched, treat this as the final prompt to do so.
May 4, 2026 – Update 3
A third exploitation campaign has been identified, separate from Sorry Ransomware and the Mirai botnet variant. According to The Hacker News, an unknown threat actor used CVE-2026-41940 to target government and military entities in Southeast Asia, specifically Philippine government and military domains (*.mil.ph, *.ph) and Laotian government domains (*.gov.la), as well as MSPs and hosting companies in the Philippines, Laos, Canada, South Africa, and the United States. The actor deployed the AdapdixC2 command-and-control framework with OpenVPN and Ligolo for persistent access and network pivoting, using IP 95.111.250[.]175 as the primary attack source.
BleepingComputer has confirmed additional technical details on the Sorry Ransomware campaign: the encryptor is Go-based, runs on Linux, and uses ChaCha20 stream cipher encryption with RSA-2048 key protection.
Cloudflare deployed an emergency WAF rule on April 30 specifically for this vulnerability, labeled “cPanel – Auth Bypass – CVE:CVE-2026-41940”, blocking malicious traffic at the network edge. Cloudflare customers with the WAF enabled had partial mitigation in place from April 30, before patches had fully propagated across provider infrastructure.
May 4, 2026 – Update 2
The Shadowserver Foundation posted on May 1 that “at least 44K IPs [are] likely compromised and seen scanning our honeypots” as of April 30. This is Shadowserver’s own characterization, not an editorial interpretation: their public dashboard defines the dataset as “cPanel instances likely compromised via CVE-2026-41940 and seen scanning, launching exploits, or brute-forcing against our sensors.” The figure represents IPs that are both assessed as likely compromised and actively being used as attack infrastructure. The Censys count of 7,135 hosts with .sorry ransomware files remains the hard lower bound for confirmed ransomware deployment specifically.
The Shadowserver dashboard published a geographic breakdown for April 30: United States 15,200, France 4,300, Germany 4,200, United Kingdom 2,300, India 2,100, Canada 2,100, Netherlands 2,000, Singapore 1,800, Indonesia 1,700, Australia 1,000, with additional activity in Japan, Poland, Spain, Ukraine, Turkey, Brazil, South Africa, and Bangladesh. SecurityWeek notes that exploitation activity dropped significantly by May 3 as the patch cycle completed across major providers, and that the spike in activity correlated directly with watchTowr’s publication of the full technical breakdown.
Three additional patched versions confirmed by SecurityWeek not previously listed: 11.86.0.41, 11.124.0.35, and 11.130.0.19. The full patched version list has been updated in the Affected Versions section below.
May 4, 2026 – Update 1
2FA did not protect against this vulnerability. watchTowr’s technical breakdown of CVE-2026-41940 confirms that the exploit injects tfa_verified=1 directly into the session file as part of the attack chain, bypassing two-factor authentication entirely. Operators who had 2FA enabled on WHM and assumed that protected them from unauthenticated access were not protected. This applies to any account on an unpatched server during the February 23 to April 28 exposure window.
watchTowr describes the attack as wormable: fully unauthenticated exploitation at scale across 1.5 million exposed instances requires no modification to the base exploit. The firm estimates approximately 70 million domains were affected across the exposed instance base, consistent with the 1.5 million server figure given the multi-tenant nature of shared hosting.
Picus Security has published detection IOCs for the exploit. Indicators to check in logs and session files:
- Session files in
/var/cpanel/sessions/raw/containing embedded\ror\nin password fields - Sessions with
hasroot=1ortfa_verified=1paired withorigin_as_string=...method=badpass - Access logs showing 307 redirects to
/cpsessXXXXXXXXXX/without a preceding successful login POST - Cookies formatted as
whostmgrsession=:<name>on Basic-auth requests
The CISA federal agency remediation deadline of May 3 has now passed. Federal agencies that had not patched by that date are in violation of the KEV catalog directive. For commercial hosting providers, enterprise and government clients operating under security frameworks that reference the KEV catalog now have grounds to request documented proof of remediation and forensic review of the February-April exposure window.
What Happened and When
CVE-2026-41940 is a CVSS 9.8 CRITICAL authentication bypass in cPanel and WHM, classified as CWE-306 (Missing Authentication for Critical Function). It was exploited in the wild from at least February 23, 2026, patched on April 28, 2026, and added to CISA’s Known Exploited Vulnerabilities catalog on April 30, 2026. The gap between first known exploitation and public advisory is 64 days.
KnownHost CEO Daniel Pearson confirmed exploitation attempts dating to February 23. hosting.com’s incident communications on April 28 described the vulnerability as having been “responsibly disclosed to cPanel” before the public advisory. The most likely reconciliation: attackers discovered and exploited the vulnerability independently, weeks or months before the researcher who performed the responsible disclosure. There was no CVE, no public advisory, and no vendor alert between February 23 and April 28. Standard vulnerability scanners had nothing to match against.
cPanel has not addressed the February exploitation date in any public communication.
How the Exploit Works
The vulnerability combines three weaknesses in cPanel’s session handling. First, the Basic-auth handler in cpsrvd failed to call the CRLF-stripping function (filter_sessiondata()) before saving sessions, despite other code paths doing so. Second, when a session’s hex obfuscation component was stripped from the cookie, the encoder skipped encryption and wrote passwords in plaintext. Third, sessions exist in both raw text files and JSON caches, and injected data transforms differently between the two representations.
The attack chain in five steps: trigger a failed login to generate a legitimate session; submit a Basic Authorization header with embedded newlines in the password field; craft CRLF injection to write attacker-controlled lines including hasroot=1, tfa_verified=1, and user=root; trigger the “token denied” handler which re-parses the raw file and promotes injected lines into the JSON cache; the injected successful_internal_auth_with_timestamp property bypasses password validation entirely.
The patched files are Cpanel/Session.pm, Cpanel/Session/Load.pm, and Cpanel/Session/Encoder.pm.
Affected Versions and Patches
The vulnerability affects all cPanel and WHM versions from 11.86.0 through 11.136.0 and WP Squared v136.1.7 and earlier. Patched versions by release branch:
- 11.86.x: update to 11.86.0.41
- 11.110.x: update to 11.110.0.97
- 11.118.x: update to 11.118.0.63
- 11.124.x: update to 11.124.0.35
- 11.126.x: update to 11.126.0.54
- 11.130.x: update to 11.130.0.19
- 11.132.x: update to 11.132.0.29
- 11.134.x: update to 11.134.0.20
- 11.136.x: update to 11.136.0.5
Scale of Exposure
Rapid7 identified approximately 1.5 million internet-exposed cPanel instances using Shodan. Censys independently counted 1,052,657 cPanel and WHM hosts on the internet. watchTowr estimates approximately 70 million domains were affected across those instances. Each server hosts multiple customer accounts, domains, databases, and email addresses, making the downstream exposure considerably larger than the host count alone suggests.
Hosting M&A Consultation
Get one-on-one advice on maximizing your hosting company’s valuation and navigating the sale process.
Active Exploitation Campaigns
Censys data shows the scale of post-disclosure weaponization. On May 1, 15,448 cPanel and WHM hosts were observed participating in malicious activity, representing 79.99 percent of all malicious hosts tracked by GreyNoise that day. The prior day’s figure was 146. The 100-fold increase in 24 hours reflects automated exploitation at scale.
Two distinct campaigns are active. The first deploys Sorry Ransomware, which renames files with a .sorry extension and leaves a ransom note referencing the qTox communication tool. The .sorry extension has previously been associated with a Hidden-Tear variant of the ransomware. Censys identified 7,135 cPanel and WHM hosts showing .sorry extensions. WordPress core files are specifically targeted: wp-config.php, wp-cron.php, wp-load.php, and wp-settings.php appear most frequently in the renamed file list.
The second campaign deploys a Mirai botnet variant identified as “nuclear.x86.” A community report from r/cpanel documents a concrete case: a brand-new dedicated HostGator server with cPanel, not yet loaded with any customer content, was compromised on April 29 at 22:59, hours after the public advisory. The shell history showed the attacker downloading nuclear.x86 from 87.121.84.78, executing it, then deleting the binary. The server had logged 2,481 failed login attempts since the last legitimate access. The provider declared the server dirty and refunded the service.
The broader infrastructure targeting cPanel is not new. The Brutus Botnet, first documented in March 2024, has been targeting cPanel ports 2082 and 2083 as part of a large-scale campaign across VPN appliances, RDP, and web applications. In March 2025, EclecticIQ connected Brutus to Black Basta ransomware operations, identifying it as an automated foothold generator for ransomware-as-a-service affiliates. Community-sourced blocklists of IP addresses observed attempting CVE-2026-41940 exploitation are circulating in hosting operator communities.
Among cloud and hosting providers, Censys identified the highest concentrations of malicious cPanel hosts at: DigitalOcean (1,043), Contabo (716), OVH (501), Vultr (391), Oracle (321), Unified Layer (280), Hetzner (277), Akamai Linode (275), GoDaddy (209), Microsoft (169). These figures correlate with where cPanel is most widely deployed and should not be read as reflecting provider-specific security failures.
What the CISA Listing Means
CISA’s Known Exploited Vulnerabilities catalog is reserved for vulnerabilities with confirmed active exploitation. CVE-2026-41940 was added on April 30 with a federal agency remediation deadline of May 3. That deadline has now passed.
For commercial hosting providers, the CISA listing has a direct practical implication: enterprise and government clients operating under security frameworks that reference the KEV catalog now have compliance-level grounds to request documented proof of remediation and a forensic account of what occurred during the February-April exposure window. Providers who took cPanel offline promptly on April 28 and patched that day have a defensible timeline. Providers who did not will face harder questions.
What to Do Now
If you have not yet patched, update to the patched version for your release branch immediately using the table above.
If your server was accessible on cPanel ports between February 23 and April 28, treat it as potentially compromised regardless of patch status. The recommended approach for confirmed or suspected compromise is migration to a clean installation using pre-breach backups, not manual cleanup. NocInit’s response guidance for CVE-2026-41940 states the case directly: “Modern post-exploitation toolkits are designed specifically to survive cleanup: rootkits hide in kernel modules, persistence is split across multiple unrelated locations.”
For servers where compromise is suspected but not confirmed, run a full audit covering:
- Session files in
/var/cpanel/sessions/raw/and/var/cpanel/sessions/cache/for the IOCs listed in the May 4 update above - SSH authorized keys in
/root/.ssh/authorized_keys - Cron entries across
/etc/cron.d/,/etc/crontab, and/var/spool/cron/ - WHM API tokens for any unrecognized entries
- Sudoers files for unauthorized privilege grants
- New administrator accounts not created by known users
Rotate all root and WHM reseller passwords, API tokens, and SSH keys regardless of whether active compromise is confirmed. Restricting administrative ports 2082 through 2096 from the public internet at the firewall level should be treated as a permanent baseline configuration going forward.
Łukasz Nowak
Nearly two decades in IT. A decade in web hosting - and still in the trenches. Writing about the infrastructure that runs the internet from the inside.
Sources
- cPanel and WHM Security Update 04-28-2026 - cPanel Support (official advisory)
- CVE-2026-41940 - NVD / NIST National Vulnerability Database
- CVE-2026-41940: cPanel and WHM Authentication Bypass - watchTowr Labs
- CVE-2026-41940 cPanel and WHM Authentication Bypass - Rapid7
- CVE-2026-41940 Explained - Picus Security
- The cPanel Situation - Censys
- Critical cPanel Vuln Hits CISA - The Register
- cPanel Authentication Bypass Being Exploited - CyberScoop
- cPanel Zero-Day Vulnerability Exploited - Help Net Security
- CVE-2026-41940 Response Guide - NocInit
- The Brutus Botnet - Annoyed Engineer
- AL26-008 - Canadian Centre for Cyber Security
- Actively Exploited cPanel Bug - Malwarebytes
- Over 40,000 Servers Compromised in Ongoing cPanel Exploitation - SecurityWeek
- Shadowserver Public Dashboard: cPanel CVE-2026-41940 (April 30, 2026)
- Critical cPanel Vulnerability Weaponized to Target Government and MSP Networks - The Hacker News
- Critical cPanel Flaw Mass-Exploited in Sorry Ransomware Attacks - BleepingComputer
- CVE-2026-41940: Full Technical Details and InMotion's Response - InMotion Hosting
- WAF Emergency Release 2026-04-30 - Cloudflare
- cPanelSniper: CVE-2026-41940 Exploitation Framework - GitHub
- Sorry Ransomware Victims: cPanel Zero-Day CVE-2026-41940 Attack Analysis - I Am Tzar
- South-East Asian Military Entities Targeted via cPanel (CVE-2026-41940) - Ctrl-Alt-Intel
- Multiple Threat Actors Actively Exploit cPanel Vulnerability (CVE-2026-41940) - Help Net Security
- Hackers Are Still Exploiting the cPanel Bug to Gain Control of Thousands of Websites - TechCrunch